Nigeria’s digital infrastructure is facing a new kind of threat, one that not only disrupts systems but quietly extracts and weaponises the data that underpins them. The recent cyber incident at the Corporate Affairs Commission marks an escalation in the crisis.
The CAC is the statutory body responsible for company registration and corporate identity in Nigeria. It sits at the centre of the business ecosystem. Any compromise of its systems is not merely a technical failure; it is a breach of the trust architecture that supports commerce, regulation, and legal identity.
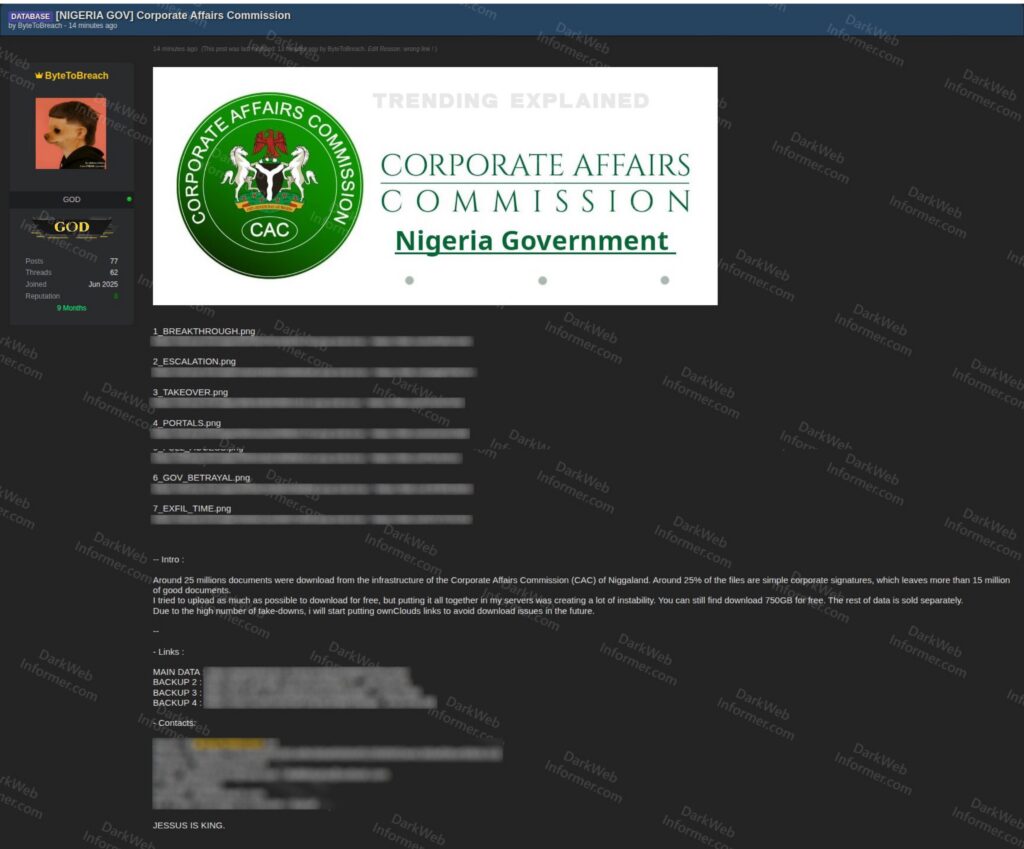
The commission has recognised that someone accessed its systems without permission, and investigations suggest a significant breach connected to a fast-growing cybercriminal group called ByteToBreach.
The full statement from the Commission reads as follows: “The Corporate Affairs Commission (CAC) is currently reviewing a cybersecurity incident involving unauthorised access to limited aspects of its information systems.
“The Commission promptly activated its response protocols and is working with the National Information Technology Development Agency (NITDA), relevant government agencies and partners to assess the scope and impact.
Advertisement
“Appropriate containment measures have been implemented, and additional safeguards are in place. While the review is ongoing, stakeholders are advised to monitor their records on the CAC portal, update their login credentials, and remain cautious of unsolicited communications.
“CAC remains committed to the security and integrity of Nigeria’s corporate registry and will provide updates as necessary.”
ByteToBreach is not a conventional hacking group with a visible structure, ideology, or leadership hierarchy. It operates as a pseudonymous entity, likely comprising a small, highly efficient unit or even a single orchestrator supported by a loose network of collaborators.
They famously created a professional-looking WordPress site under the name “Pentesting Ltd”. It mimics a legitimate security firm, but it’s actually used for victim-shaming.

Advertisement
The actor first appeared in the global cybercrime ecosystem around mid-2025 and quickly built a reputation through high-impact breaches and the aggressive marketing of stolen datasets.

Unlike traditional ransomware groups that focus on encrypting systems and demanding payment for restoration, ByteToBreach belongs to a newer class of operators whose primary objective is data exfiltration.
Their model is built around stealing, packaging, and monetising sensitive information, often without visibly disrupting the victim’s operations.
The CAC breach appears to follow this established operational pattern.
Rather than simply gaining access to systems, the attacker is believed to have penetrated deeper layers of the commission’s digital infrastructure, potentially exploiting weaknesses in APIs or database access controls.
Advertisement
Reports indicate that the accessed data may include highly sensitive materials, such as identity documents, photographs, signatures, and corporate registration records. Such data is particularly valuable because it forms the backbone of legal and financial identity in Nigeria.
If such datasets are indeed compromised at scale, the implications would extend far beyond the immediate breach. It would create opportunities for long-term exploitation across multiple sectors.
What makes the incident worrisome is the trajectory of attacks attributed to ByteToBreach.
Before targeting the CAC, the actor had already been linked to breaches involving financial platforms and banking infrastructure in Nigeria, including systems connected to Sterling Bank and Remita.

Other notable breaches include a ticketing platform used by Eurofiber France, which suffered data exposure and leaks in November 2025.
Before Nigeria, they had already hit banks, airlines, government entities, universities, telecommunications infrastructure, and other targets across Europe, Central Asia, and North America.
The actor claimed responsibility for several sensitive data thefts and breaches involving organisations like ICICI Prudential Mutual Fund, RDP (a PayU company), University of California, Ministry of Health of Panama, Nokia, Seychelles Commercial Bank, PKO Bank Polski (the largest bank in Poland), Uzbekistan Airways, euroAtlantic Airways, Avatel Telecom, Broadband Tower, Universidad Nacional Autonoma de Mexico, National Oil Eithopia, etc.



Those incidents reportedly exposed customer records, financial data, and identity credentials, signalling a deliberate focus on high-value targets within the country’s financial ecosystem.
The operational ecosystem supporting ByteToBreach is sophisticated and decentralised. The actor actively participates in dark web forums, where they advertise and sell stolen datasets and system access.
These forums serve as primary marketplaces, allowing the actor to reach a global pool of buyers ranging from fraudsters to other cybercriminal groups.
Complementing these activities is the use of encrypted messaging platforms such as Telegram, which function as negotiation channels and distribution hubs for data samples.
Once data is exfiltrated, it is categorised based on value, with identity-linked information, such as national IDs, financial credentials, and authentication data, occupying the highest tier.
The data can be sold directly to buyers, repackaged into smaller datasets for repeat sales, or used as leverage in extortion attempts against the victim organisation.
In many cases, access to compromised systems is also sold, enabling other actors to conduct their operations.
The result is a layered revenue model in which a single breach can generate income through multiple channels over an extended period.
The response from Nigerian institutions has followed a familiar pattern seen in high-profile breaches globally.
The CAC has initiated containment measures and engaged relevant cybersecurity agencies, while regulatory bodies such as the Nigeria Data Protection Commission and the Central Bank of Nigeria are expected to play oversight roles. However, public disclosures often lack detail, as is frequently the case.
The broader implications of the CAC breach are profound. Hacking a main source of company and personal information could allow the attacker to pretend to be a company, file fake documents, and carry out complicated fraud schemes based on
Financial institutions that rely on CAC data for verification may find their processes undermined, while businesses and individuals face increased exposure to targeted attacks.
The long-term risk is not just in what data was accessed, but also in how it may be used in the future as part of evolving fraud operations.
ByteToBreach does not operate in isolation but within a networked marketplace that amplifies the impact of each breach. The CAC incident could be part of a larger pattern that is likely to continue.
Addressing this threat requires more than reactive measures; it demands proactive cybersecurity, stronger regulatory enforcement, and sustained investment in the protection of national data assets.
Without such changes, the attacks would continue with consequences that extend far beyond any single breach.
